
The New Bedrock of Civilization
The digital architecture of our world has undergone a profound transition. What was once considered a supporting utility for commerce and communication has solidified into the very bedrock of global civilization. This transition necessitates a radical redefinition of cybersecurity. In this hyper-connected landscape, security is now a comprehensive strategic framework essential for keeping the economy stable and safeguarding a country’s independence.
The 2026 threat landscape is dominated by two primary forces, notably non-deterministic artificial intelligence (AI) and accelerating quantum computing. Organizations are no longer just protecting data packets but are managing digital trust across a volatile ecosystem of human identities, autonomous software agents, and cyber-physical systems. This shift from reactive perimeter defense to proactive, identity-centric resilience is no longer optional in today’s environment, the cost of systemic failure is measured in the potential paralysis of critical life-sustaining infrastructure.
Theoretical Foundations: Re-imagining the CIA Triad
While the technological medium has shifted, the core of cybersecurity remains anchored in the foundational CIA Triad (Confidentiality, Integrity, and Availability). However, the application of these principles in 2026 has been forced to adapt to a world where AI models and autonomous agents are the primary users of data.
Confidentiality has evolved from simple access control into a sophisticated practice of identity-based role management. With AI-powered social engineering reaching unprecedented levels of realism, traditional credentials have become liabilities. Integrity has moved to the forefront of the agenda, specifically regarding data poisoning. As autonomous systems make decisions based on massive datasets, ensuring those datasets remain untampered with is critical to preventing catastrophic algorithmic bias. Finally, Availability is now a matter of public safety. In an era where power grids and medical systems are fully digitized, resilience through redundancy is the only viable path forward.
The DAD Counter-Framework
To better understand adversarial objectives, security professionals in 2026 frequently utilize the DAD triad (Disclosure, Alteration, and Denial) as a mirror to the CIA objectives. This helps in modeling how sophisticated actors target the secrecy, accuracy, or accessibility of an enterprise’s most valuable digital assets.
| Security Objective | Targeted Principle | Adversarial Action | 2026 Risk Context |
|---|---|---|---|
| Confidentiality | Secrecy | Disclosure | AI-driven exfiltration of strategy |
| Integrity | Accuracy | Alteration | LLM training set poisoning |
| Availability | Access | Denial | Ransomware targeting smart grids |
Rise of Agentic AI and Autonomous Offense
The defining characteristic of 2026 is Agentic AI. These autonomous software entities independently plan and execute multi-step tasks. These agents interact using modern standards like the Model Context Protocol (MCP), moving across cloud tools and internal databases to execute business logic. However, this integration has introduced a new class of non-deterministic risks. Security paradigms have shifted from blocking to guiding, as Chief Information Security Officers (CISOs) seek to enable trusted autonomy.
Conversely, adversaries have operationalized AI to create Ransomware. This model uses AI for every stage of the attack lifecycle, from generating hyper-personalized deepfake phishing videos to mutating malware code on the fly to bypass behavioral analytics. These attacks compress human intervention windows to near zero. Organizations now deploy Autonomous SOCs to respond at machine speed.
Quantum Emergency: Cryptographic Agility
Quantum computing has moved from academic theory to an immediate operational priority. Adversaries now run Harvest Now Decrypt Later (HNDL) campaigns, stealing encrypted data today so they can decrypt it once quantum processors mature.
In response, the National Institute of Standards and Technology (NIST) has finalized standards for Post-Quantum Cryptography (PQC). Organizations in 2026 are focusing on cryptographic agility, the architectural ability to swap out encryption algorithms without disrupting the entire enterprise stack. For critical infrastructure, hybrid models that combine classical RSA/ECC with PQC are becoming the global standard to maintain performance while ensuring future-proof security.
Identity: The Final Perimeter
With the dissolution of traditional network boundaries, identity has emerged as the central control plane. Passwords have been effectively replaced by liveness biometrics and device-bound passkeys. Because deepfake technology can now spoof static biometrics on modern systems that require multi-frame facial muscle analysis to verify a presence during high-stakes authentication.
Furthermore, the Identity of Things (IDoT) has become vital. In 2026, every machine, sensor, and AI agent is treated as a first-class identity. This requires Zero Trust Architecture (ZTA), where systems never grant implicit trust, and JIT privileges restrict access strictly to the duration of each task.
Economic Resilience and Regulatory Landscapes
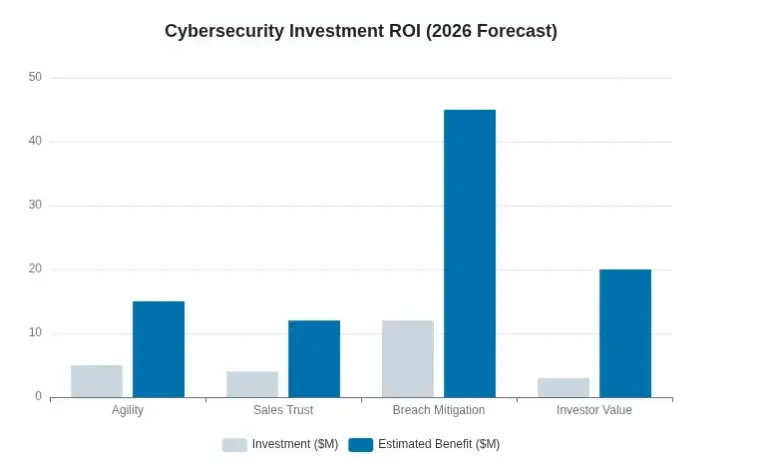
Cybersecurity is viewed as a fundamental driver of business value. Global investment in privacy and data governance has surged, with a significant percentage of organizations reporting that proactive security investments directly accelerate sales cycles and investor confidence. In 2026, 99% of organizations report measurable ROI from their privacy programs, often totaling millions of dollars in annual benefits.
Source: worldeconomics.com
Regulatory frameworks have also matured. In India, the Digital Personal Data Protection (DPDP) rules are now fully operational, mandating verifiable consent and itemized notices. In the In the European Union, NIS2 and DORA have introduced personal liability for board members. Cyber risk oversight is now a fiduciary responsibility. Meanwhile, the United States is following suit. New York’s Child Data Protection Act now mandates a security-by-design approach for vulnerable populations.
Conclusion
Cybersecurity in 2026 has moved beyond protecting data. Today, it preserves societal function itself. The dual pressures of autonomous AI and quantum threats have forced a return to first principles anchoring resilience in identity, data integrity, and architectural agility. Thriving organizations view security as an enabler, not a barrier. It becomes the dependable layer supporting safe adoption of non-deterministic systems. The path is clear, we must build systems that resist breaking, heal automatically, and adapt in real-time.





